Phantom — AppSec Intelligence Platform
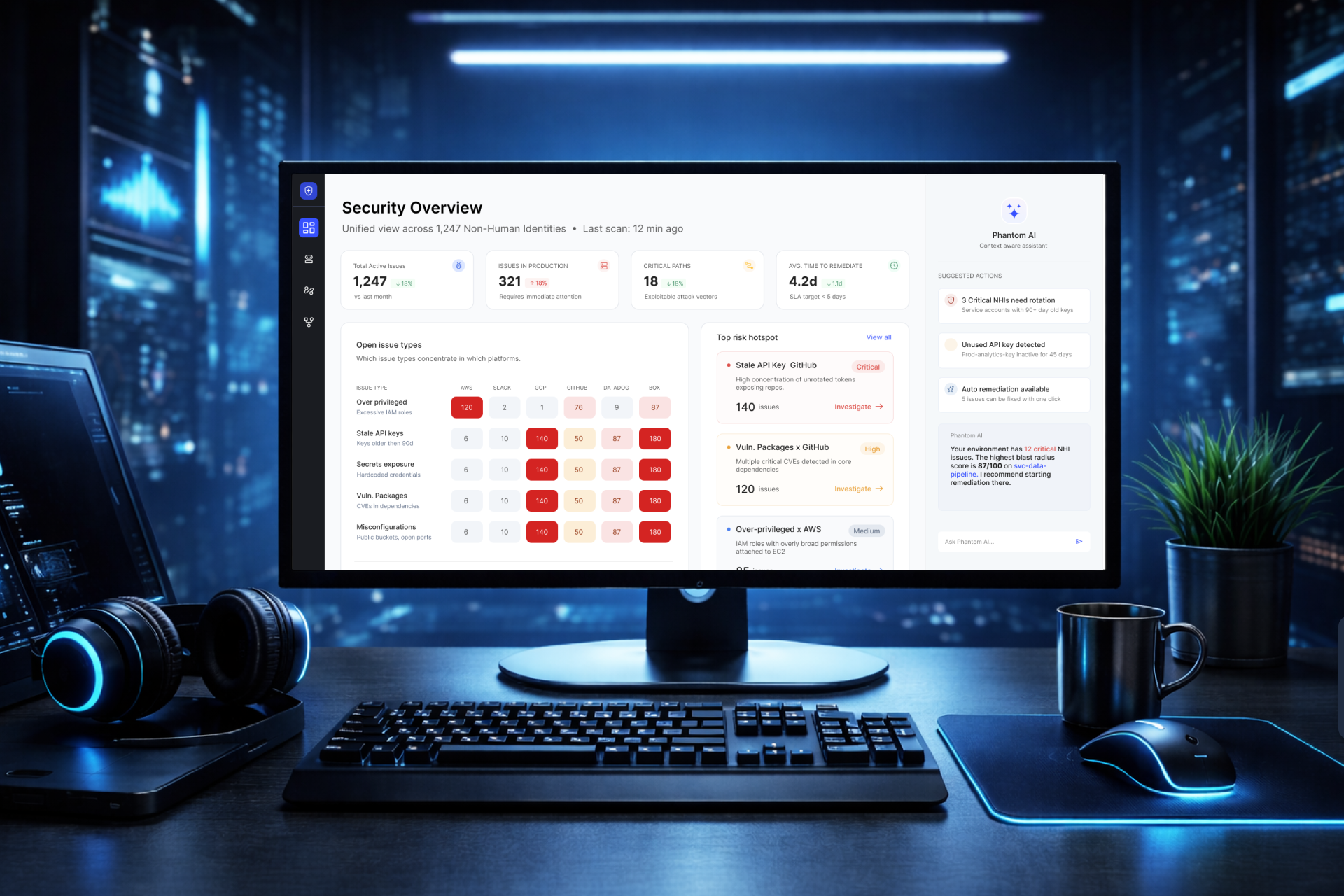
Security teams don't lack data — they lack clarity. Phantom connects fragmented security signals into a unified view of risk across code, pipelines, and production.
Security teams don't lack data — they lack clarity. Phantom connects fragmented security signals into a unified view of risk across code, pipelines, and production.
Organizations rely on multiple security tools: code scanning (SAST), CI/CD security, cloud security, secrets detection, and identity systems. Each generates alerts. None of them are connected.
The result:
Security teams couldn't answer the questions that matter most: Which issues actually matter right now? Which ones reached production? Where is risk concentrated?
The opportunity wasn't to build another dashboard — it was to fundamentally change how security teams understand risk. Instead of treating issues individually, Phantom treats risk as a system.
From isolated alerts → to connected risk intelligence.
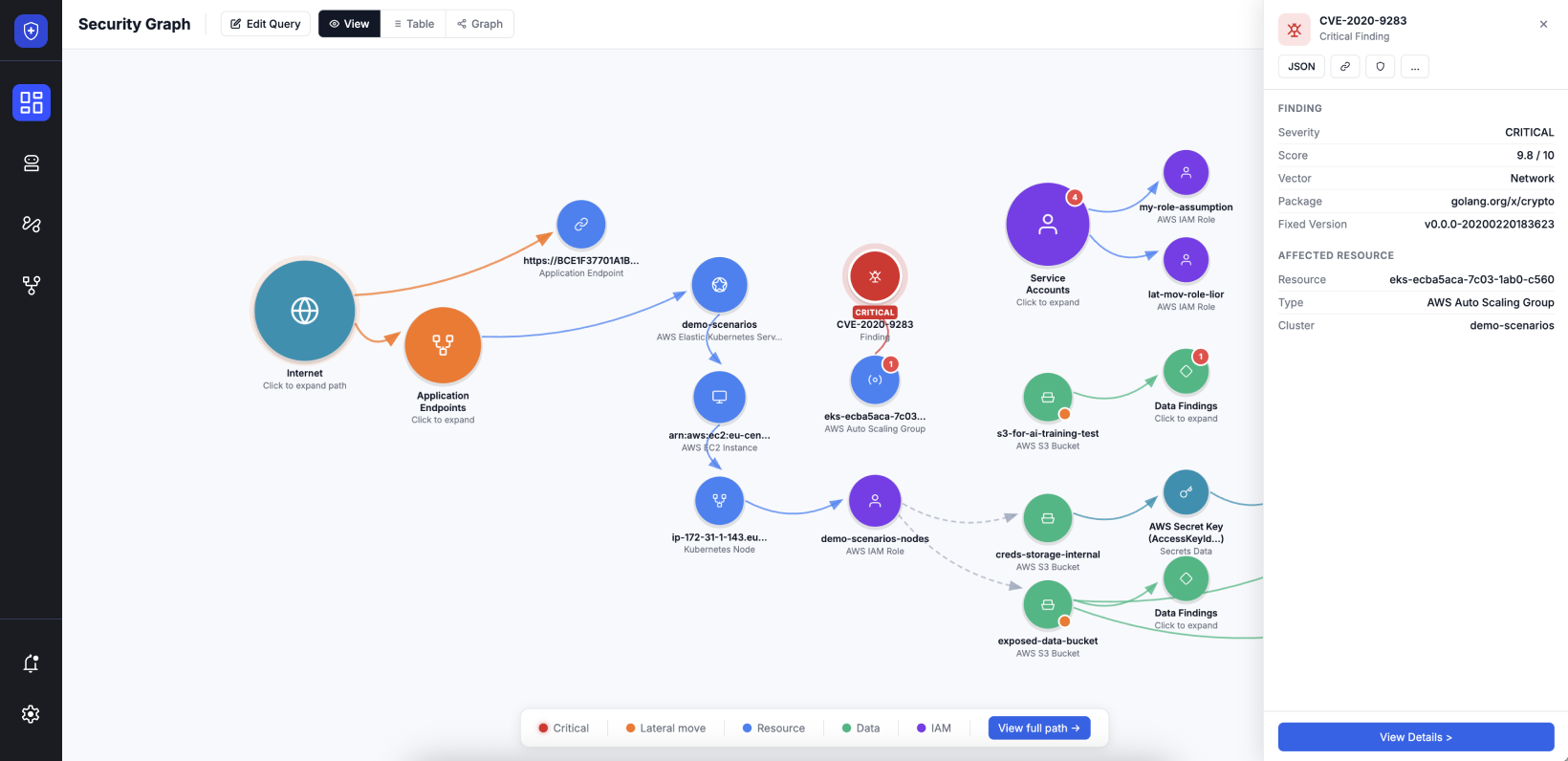
Phantom introduces a new way to understand security by connecting issues across the entire lifecycle — from code to CI/CD to production — and surfacing only what truly matters.
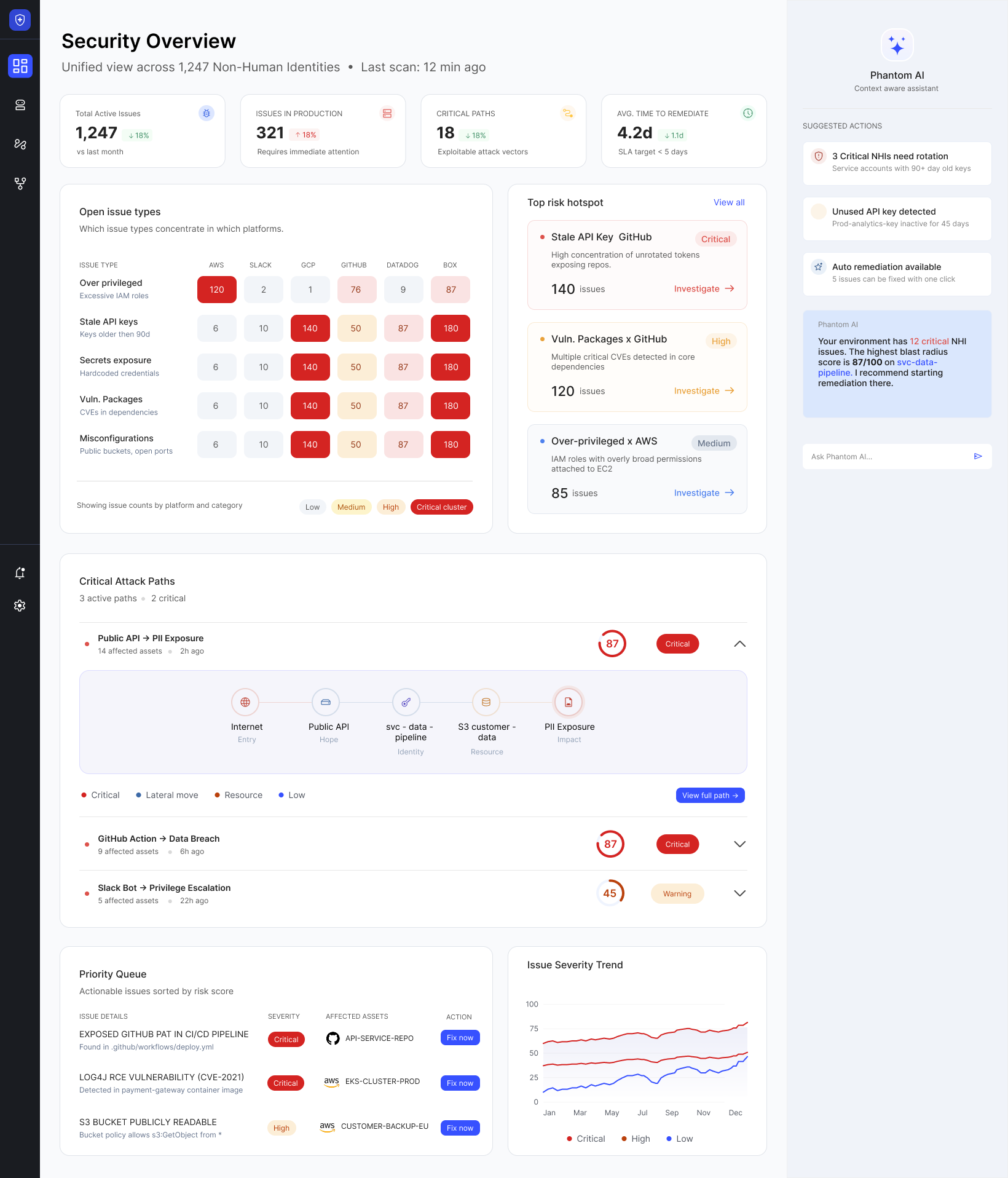
Traditional dashboards show numbers. Phantom shows risk distribution. The heatmap maps issue types × platforms — highlighting concentration of risk and surfacing systemic problems instantly.
Heatmaps show patterns — but users need direction. A focused panel highlights the highest risk concentrations, combining signals from type, platform, and volume for instant prioritization without analysis overhead.
Most dashboards stop at insights. Teams need actions. A prioritized list based on exposure, reachability, and business impact — each item includes context, ownership, and a recommended action.
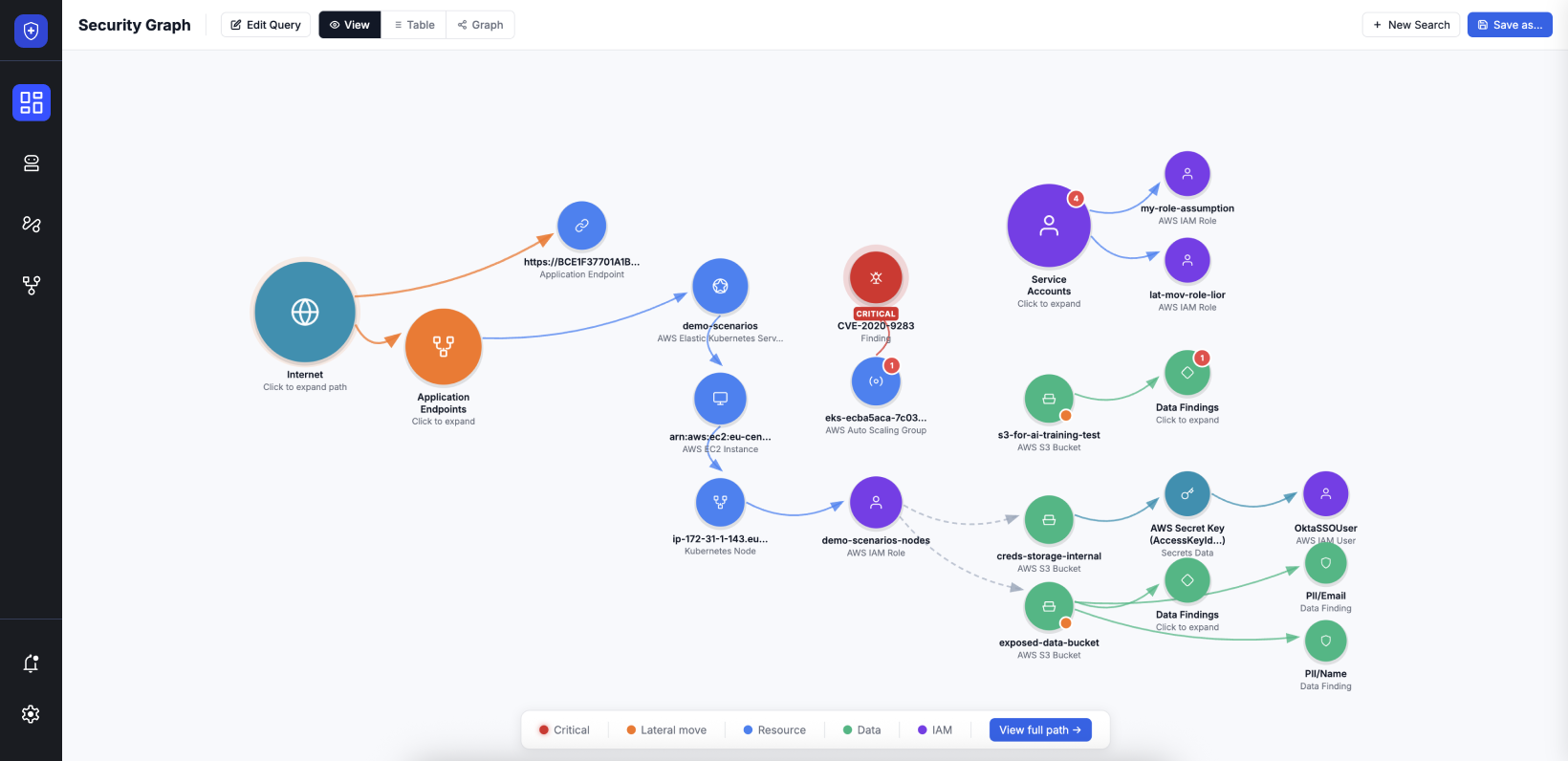
Security issues don't appear — they propagate. A flow-based visualization traces risk from Code → CI/CD → Production, revealing where risk started, how it moved, and where intervention failed.
Remove noise, highlight what matters. Less is more when stakes are high.
Connections matter more than counts. One connected insight beats a hundred isolated alerts.
Every insight leads to a decision. The interface doesn't stop at showing — it drives doing.
Security tools generate massive datasets with no built-in hierarchy. Solution: abstraction and aggregation — surface patterns, not raw numbers.
Each system works in isolation with its own schema and severity model. Solution: a unified data model concept that normalizes signals across all tools.
Severity alone doesn't reflect real risk — a low-severity issue in production can be more dangerous than a critical one in dev. Solution: combine exposure, propagation, and business impact.
Security teams can answer critical questions independently
Risk is visible across the full development lifecycle
Prioritization is driven by impact — not just severity
Teams shifted from reactive to preventive security workflows
This project demonstrates my ability to: